Detect. Decrypt. Deter.
Encrypted Traffic Orchestration without Compromise
Addressing Visibility Challenges with TLS 1.3
Mira Security is working with the National Institute of Standards and Technology’s (NIST’s) National Cybersecurity Center of Excellence (NCCoE) on the Addressing Visibility Challenges with TLS 1.3 Project.
Introducing the World’s First Dedicated Virtual TLS Decryption Appliance for Enterprises
Sign up for your exclusive Mira vETO Virtual Decryption Appliance trial today.
Nearly all Network Traffic is Encrypted.
And Encryption Standards are Getting Tougher.
While encryption is great for ensuring privacy and data protection, current security tools are “blind” to threats carried by encrypted connections. And that gives bad actors a method to infiltrate networks.
Today, with enterprise networking moving to the cloud, and workers moving to the home, a whole new set of challenges is forcing compromises between privacy and security.
The Word “Mira” Indicates Visibility.
Mira Encrypted Traffic Orchestration (ETO) enables enterprises to remove this “blind spot” by providing visibility into encrypted traffic for the full range of security and analytic tools being used. The Mira solution addresses encryption challenges and removes bottlenecks today, and can scale with the architectures of tomorrow.
Mira provides safe and secure visibility into encrypted traffic allowing the tools used by enterprise security teams to function effectively
MIRA FEATURES
Mira ETO software enables the enterprise security stack to detect and mitigate threats while ensuring that privacy and compliance requirements can be met.
- Automatically detect all SSL/TLS and SSH traffic in the network, no matter what ports are being used
- Capable of decrypting SSL v3, TLS 1.0, 1.1, 1.2 and 1.3, as well as SSHv2
- Transparent to the higher-level protocols being carried on top of the encrypted layer providing decrypted flows to security tools for any existing or future protocols
Mira seamlessly integrates with existing security tools to protect your investments
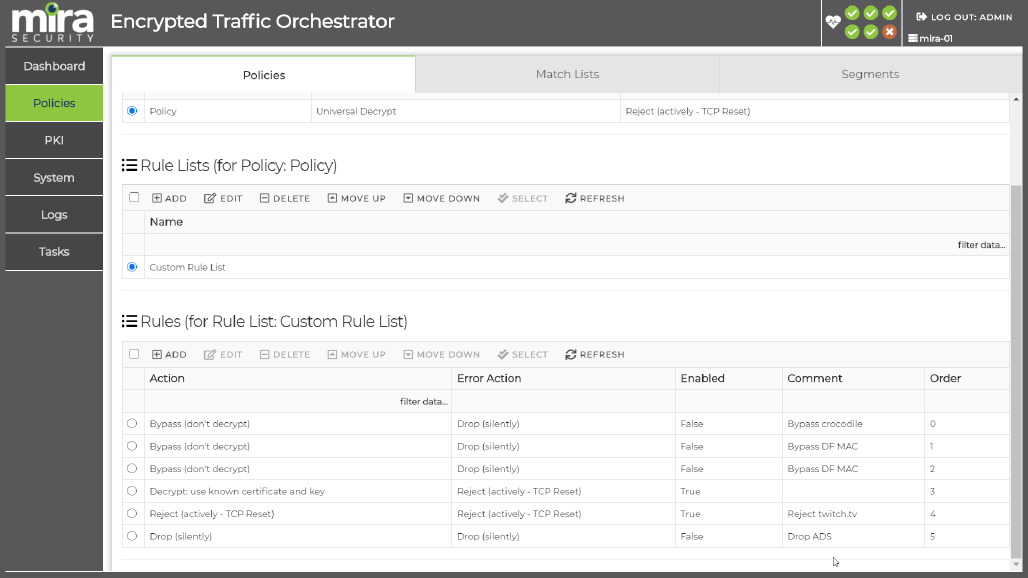
- Policy control over which encrypted traffic is made visible allows compliance with industry requirements and enterprise policies on data privacy
- Policy control over which encryption mechanisms are allowed in the enterprise network to prevent weak or obsolete methods from being used
- Comprehensive logging enables the enterprise to analyse encrypted traffic within the network and derive actionable changes to operational policy
- Scaling from a sub 1G for branch offices and micro edge locations to nearly 100G allows for growth and supports the collapsing of data centers.
Enterprises need to balance the security risks of not decrypting traffic with the privacy implications of doing so.
Mira ensures that balance is achieved.
Recent Events

RSA Conference 2025
April 28-May 1, 2025
Moscone Center, San Francisco
Booth 3333, Moscone South Expo
At RSAC 2025, you’re not just attending a conference—you’re stepping into a vibrant, thriving community of thinkers, innovators, and achievers. Though we come from different corners of the cybersecurity world, we are united by a common mission: to foresee risks, counter threats, and embrace the challenges ahead. Together, we shape the future of security. Together, we shine as one.
Mira Security and Garland Technology Webinar Series
Mira Security and Garland Technology are teaming up to offer this strategic webinar series to provide enterprises with high-level insights and deep dives into TLS 1.3 Decryption and Traffic Orchestration.

WEBINAR:
TLS 1.3 Encryption – Gaining Data Security but Losing Security Visibility?
May 16, 2024
Experts from Axellio, Mira Security, and Garland Technology discussed on how TLS 1.3 encryption negatively impacts cybersecurity visibility. They explored how security monitoring needs to transform to protect our networks and applications and discussed the importance of teaming with industry partners and U.S. Government users to address those challenges.

WEBINAR:
The TLS 1.3 Encryption Paradox: Are we strengthening end-to-end encryption but limiting cyber security monitoring?
February 22, 2024
Experts from Mira Security, Axellio, and Garland Technology discussed the TLS 1.3 encryption paradox. They also covered why decrypting traffic is essential for security monitoring, how TLS 1.3 differs from previous versions, how the approaches enterprises have taken towards decryption are changing, and more.