Orchestrate Encrypted Traffic Across the Enterprise Using Safe, Secure and Scalable Decryption.
Introducing the World’s First Dedicated Virtual TLS Decryption Appliance for Enterprises
Sign up for your exclusive Mira vETO Virtual Decryption Appliance trial today.
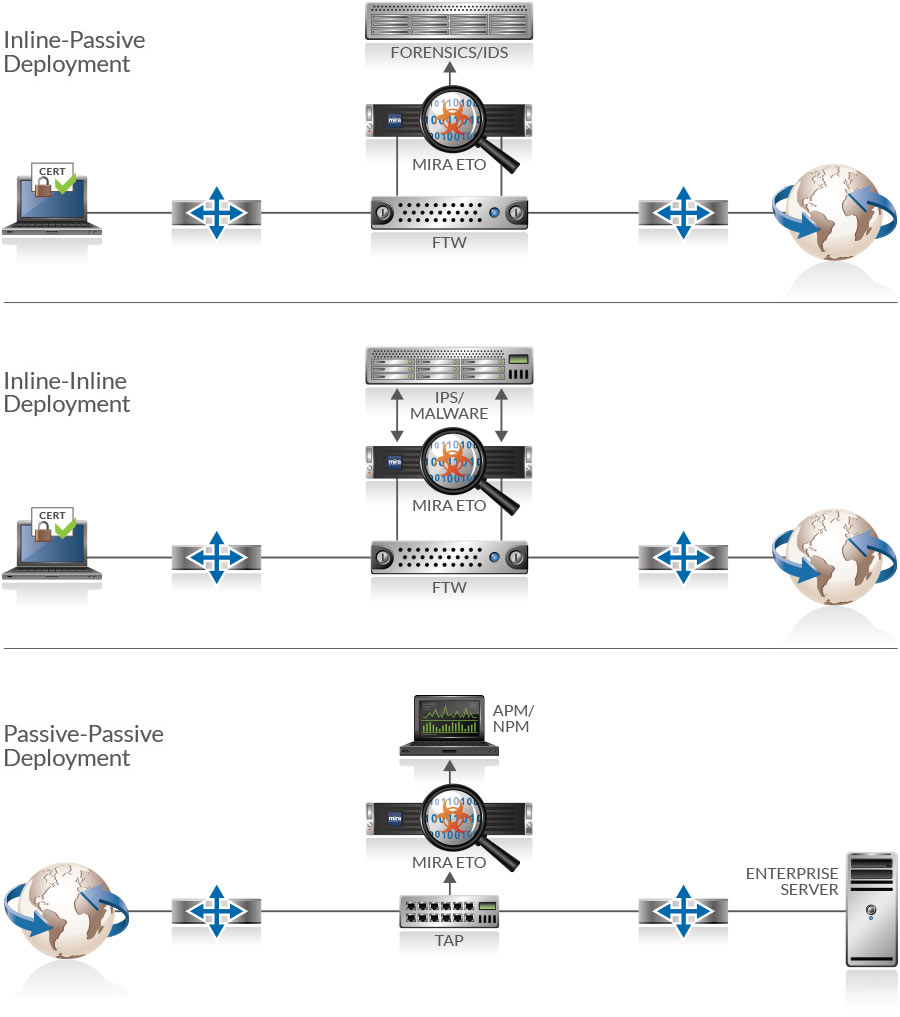
How Mira Works
Mira Encrypted Traffic Orchestration (ETO) automatically detects SSL, TLS and SSH traffic, then forwards it to your existing security tools so they can detect and mitigate potential threats. Meanwhile, no special interfaces or software changes are required—security tools receive data as if it were coming directly from the network. As a result, these tools regain their effectiveness, despite the rise in encrypted traffic, simply by integrating Mira ETO into your architecture. Furthermore, deployment is streamlined to minimize disruption and maximize visibility.
MIRA DEPLOYMENT MODES
Software Subscription License
Additionally, Mira ETO software is licensed as a subscription model. Subscriptions can be for 12 months or 36 months and can be upgraded during the subscription period. The license purchased determines the amount of encrypted traffic that can be decrypted to provide visibility for security tools.
Mira ETO Demo
In this video we see how Mira Security Encrypted Traffic Orchestration can enable your network security systems to properly monitor traffic and detect threats that they would otherwise miss due to encryption.
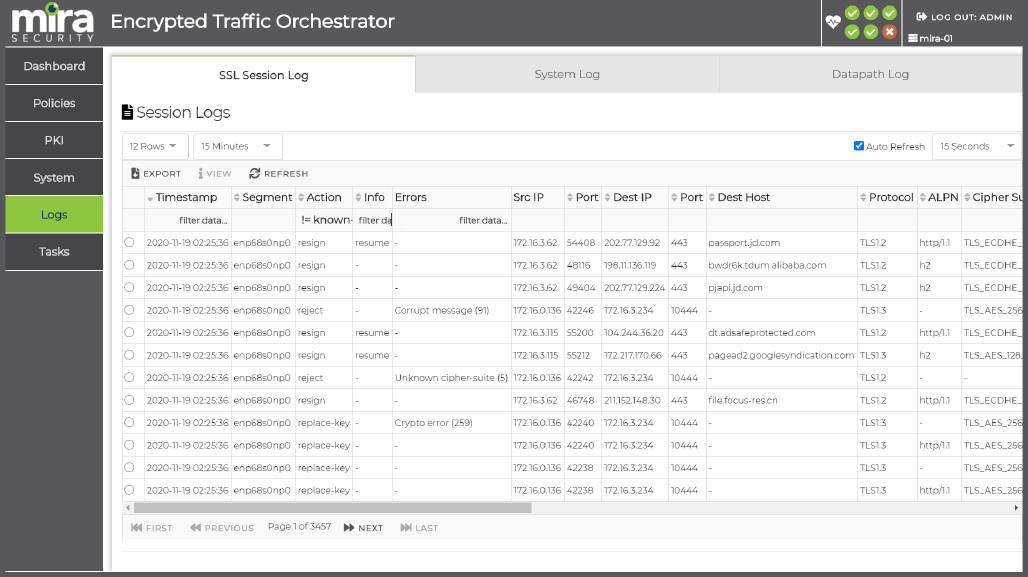
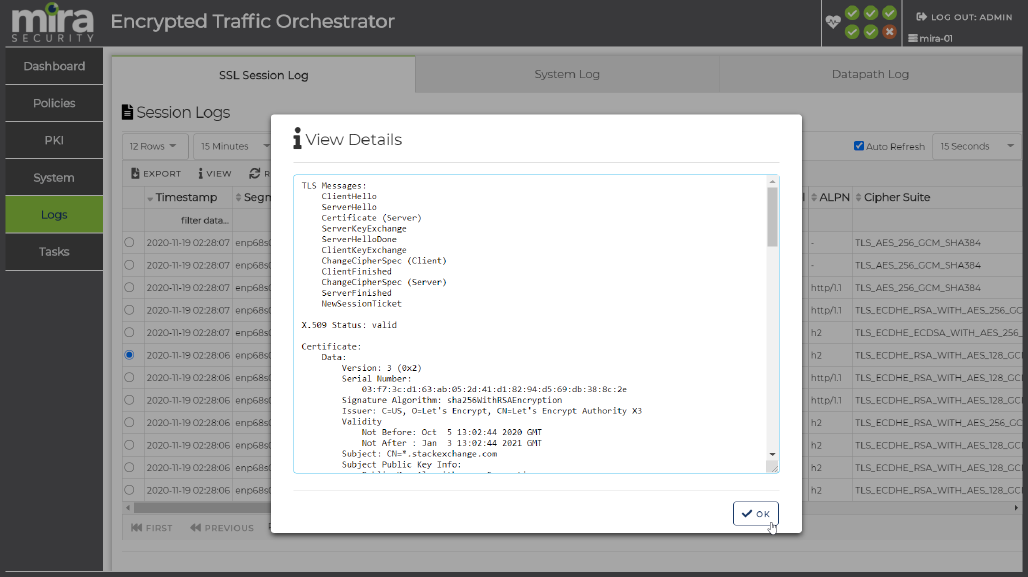
Enterprises need to balance security risks of not decrypting traffic with the privacy implications of doing so.
Mira ETO provides the flexible policy controls to ensure that balance is achieved.
Flexible policy control features of Mira ETO enable enterprises to enforce policy on what encryption mechanisms are allowed in order to ensure a secure environment. For encrypted traffic that is allowed, there are fine-grained policies that enable control over which encrypted flows are decrypted and made visible to security tools. Policy controls can optionally make use of the Mira category database and/or a locally created category database to determine which types of traffic are decrypted.
Built for high-performance decryption, the ETO software supports link speeds of 1, 10, 25, 40 and soon 100 Gbps, enabling decryption for encrypted traffic ranging from under 1 Gbps to over 100 Gbps. Mira’s ETO software supports high rates of new TLS handshakes per second, ensuring that there is no performance impact when deployed. The software is architected to allow the use of external hardware PKI engines enabling both decryption performance and new handshake performance to be scaled even higher.

Appliance Licensing
A license can be used on either a virtual appliance or on one of the hardware appliances available from Mira Security.
* Six (6) breakout segments planned for future software release.
Large ETO Deployment in Your Enterprise?
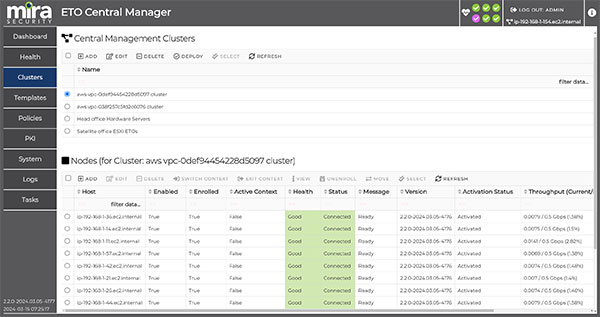
Mira Central Manager Makes It Easy.
The Mira Central Manager can manage and deploy all ETO configurations, such as PKI, policies, segments, system configuration, and licensing, as well as ETO software upgrades.
Look Deeper into Mira
Mira removes enterprise network “blind spots” by providing visibility into unencrypted connection for the full range of security and analytic tools.
Learn more about Mira by visiting our Resources page to download the Mira product brief and whitepapers, or watch videos.
Sign Up for a Mira Demo and See What You Could Be Missing.
mnemonic AS Podcast
Episode 66: Encrypted Traffic Management
TLS, SSL, HTTP, keys, authentication, clients, servers and ciphers – encryption is complicated.
To help shed some light on how enterprises can remove the “blind spot” of encrypted network communication, we’ve invited David Wells, co-founder of Netronome and Mira Security, who is a pioneer in the SSL/SSH inspection space.
David explains why being able to see and analyze encrypted traffic is necessary in order to gain full security value out of your network data, and shares his experiences since he inadvertently invented a tool for SSL inspection in 2003.